Introduction
This POV will discuss IBM’s cybersecurity solutions IBM Guardium and IBM Randori, and how they can be used individually or together to protect your IT landscape against cybersecurity threats
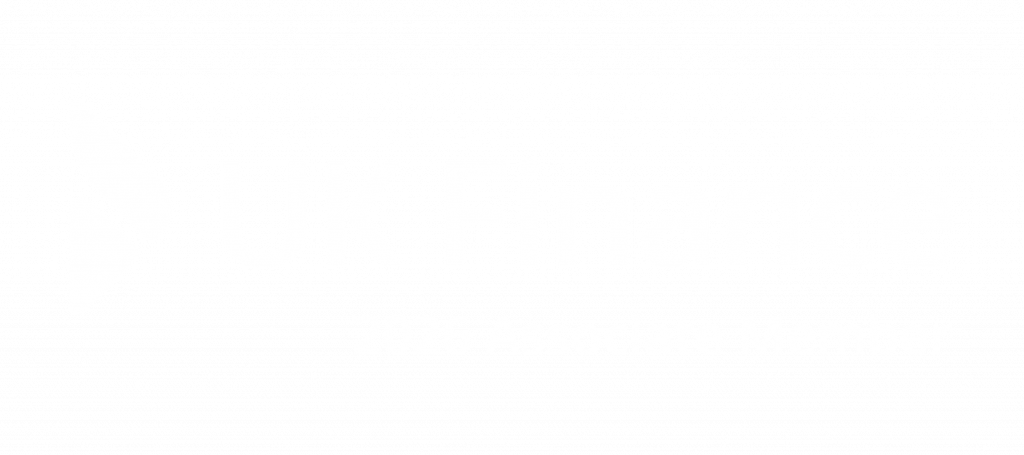
Cybersecurity has been identified as the largest priority for IT initiative in 2023, compared with cloud migration, digital transformation, customer experience, and driving business growth. Flexera note that whilst cloud migration initiatives have increased the most between 2022 to 2023, cybersecurity still dominates as the top technology initiative year on year.
Reasons for this prioritisation include the cost associated with data breaches, the regulatory need to secure data (GDPR), and the risk to brand reputation should a company expose customer data to threats.
IBM found the average cost of a data breach to be $4.45m, and 83% of organisations surveyed experienced multiple breaches – the cost adds up.
A lack of oversight, made worse by mergers and acquisitions, means organisations are blind to their vulnerabilities. Focusing on improving this oversight and understanding of how attackers view and access an organisation is critical in mitigating the risk of a cyber-attack.
Solutions
With this focus identified, what can organisations do to protect their IT landscape against cybersecurity threats?
IBM’s Cost of a Data Breach Report 2023 found that 1 in 3 (33%) breaches were identified by the organisation’s own tools or teams, compared to 67% reported by a third-party or the attacker themselves. This showcases the need to improve internal detection mechanisms to reduce and even prevent the risk of a data breach.
This idea is backed up by the finding that breaches disclosed by the attacker cost over $1m more to remediate than those found through internal detection.
IBM Guardium
IBM Guardium is a database security monitoring tool. It helps prevent data leaks from databases, data warehouses and big data environments, ensures information integrity, and automates compliance controls in line with defined rules.
All these words to say: IBM Guardium is the solution for companies who store any form of data, or are held to regulatory compliance measures and audits.
Control your data environments by applying rules and permissions on a granular, file-by-file, level; set alerts for when certain data is accessed and by whom.
Benefit
The benefits of implementing a tool such as IBM Guardium are vast.
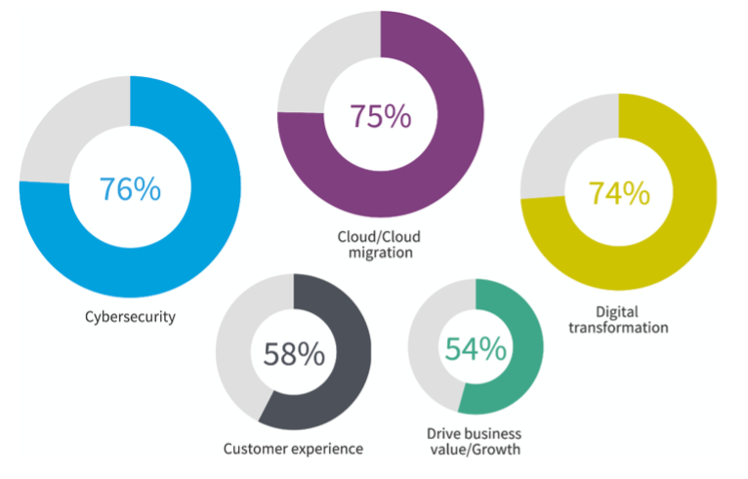
But let’s make it simple. The time to identify a data breach is where most cost is incurred. IBM find the mean time to identify is ~204 days, with a further 73 days spent containing the breach. 277 days. 277 days spent unaware of the data and cost sinkhole: the open doorway into your organisation.
Remove the passivity of data security with IBM Guardium
Detect internal and external threats by auditing activity with advanced analytics and machine-learning across all your chosen data sources, on-prem and in the cloud. Identify potential security breach cases using the Active Threat Analytics dashboard and take action to investigate and remediate.
Set up data policies to monitor data access, privileged users, application user activities, and security exceptions. Using the dynamic risk assessment capabilities, you can locate high risk users based on daily risk scores calculated based on audited data.
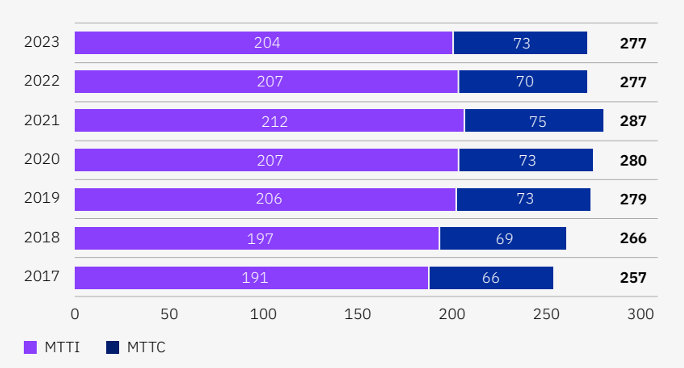
Forrester’s assessment of IBM Guardium found key benefits to include:
Ultimately, IBM Guardium provides the benefit of control and oversight of your data, based on user access, file access, or unusual trends. Secure your data the way your policies dictate, and know in advance where threats are likely to occur.
How?
IBM Guardium is set up depending on your specific requirements, with different protection options available for the type of data source you are protecting.
-
- Detect unusual activity around sensitive data. Track and flag when data is accessed in certain locations, IP ranges, or by usual individuals at abnormal times.
- Full visibility of day-to-day activity and access
- Machine learning analytics
- Automated data discovery and classification for
- data stored in databases, data warehouses and other structured data environments
- unstructured data in files and file systems
- sensitive data stored in database-as-a-service (DBaaS) platforms and cloud native platforms
- Smarter more unified data protection across hybrid cloud environments including Azure Event Hubs, AWS, Kinesis, Snowflake, SAP, MongoDB
- Vulnerability Assessment, identify threats and security gaps by automatically scanning infrastructure.
Simplify the process of managing and fulfilling compliance and privacy requirements such as GDPR, SOX, HIPPA, and DORA, by generating reports within seconds ready to share with regulators.
IBM Randori
We have discussed how IBM Guardium can secure your data environments, monitor, and alert to unusual access, and report on risky users, but how else can you minimise the risks of a data breach occurring before it is too late?
IBM Randori is IBM’s attack surface management solution.
As IT landscapes grow with the trend of digital transformation and the move to SaaS and decentralised IT buying reduces oversight of applications, the abundance of attack surfaces increases and the ability to monitor them decreases.
Monitor external surfaces for unexpected changes, blind spots, misconfigurations, and process failures with IBM Randori
A security guard continuously patrolling your entire IT estate, IBM Randori prioritises your most vulnerable attack surfaces from the perspective of an attacker.
Penetration tests are snapshots of a specific period of time, providing an unrealistic view of your attack surfaces due to the lack of real-time data and unrealistic accessibility.
30% of attack surfaces are assumed to be unknown or unmanaged
Randori runs continuously, starting with a domain name and automatically testing access until it finds a way in or identifies a threat. As your IT estate evolves, Randori scales to test access and new vulnerabilities to provide a near real-time assessment of your cybersecurity strengths and weaknesses.
Benefit
What sets IBM Randori Recon apart from the competition?
1. Authentic Discovery
Cyber criminals don’t start their attack by scanning the entire internet, and neither does Randori. Instead, it uses the same techniques attackers use, allowing us to find the IPv6 and cloud assets that others miss, from the perspective of the attacker.
2. Continuous Insight
Randori is always watching, looking for new assets and changes in your attack surface.
Identify issues quickly with Randori’s Target Temptation model (patent-pending), which updates based on attacker trends and IBM Security Randori Attack data.
3. Proactive Remediation
Understand what’s exposed, how it can be discovered, what the risk is, and what you should do – before attackers strike. Reinforce your defences before the enemy is upon you, not when it is too late.
Understanding the problem is the first step to solving it. Ignorance is bliss until the wall crumbles, and you have to pick up the (costly) pieces.
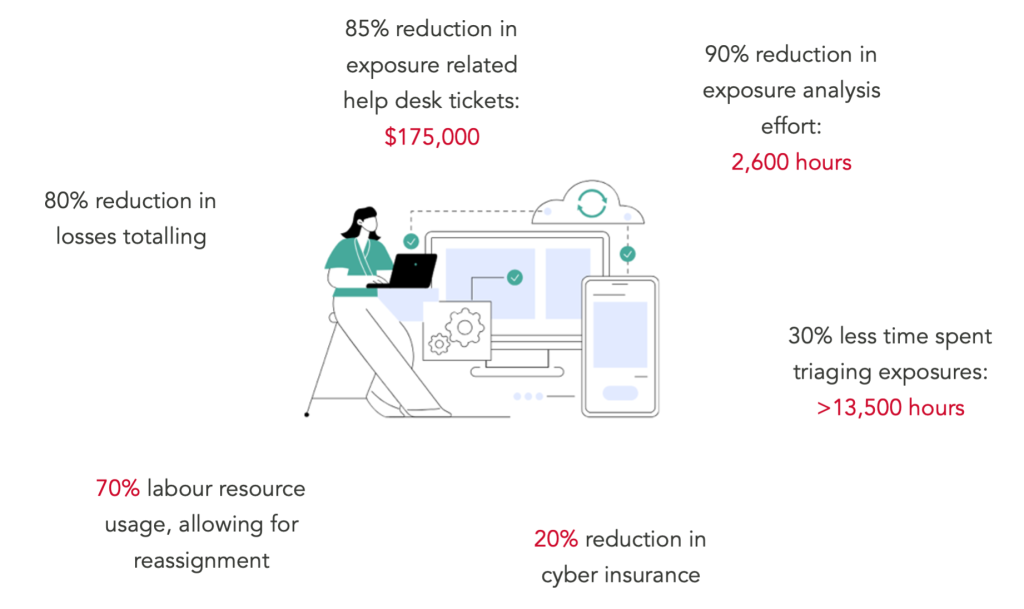
Forrester’s assessment of IBM Randori found it to shine light on shadow IT, removing the ‘unknown unknowns’ from organisations, with further key metrics including:
Understanding what the risks are is the first step towards remediating the problem. Providing oversight of an entire IT landscape from the perspective of external entities means organisations can make data-driven decisions regarding their cybersecurity and procurement choices.
Removing responsibility for monitoring attack surfaces from staff allows them to focus on other priorities, such as creating strategies to reduce attack surfaces or remove vulnerabilities.
How?
IBM Randori utilises a variety of methods to detect abnormalities in your IT infrastructure and attack surfaces.
-
- Black-Box Discovery: This approach identifies your exposed enterprise assets in a high fidelity and low impact manner and is designed for low false positives to keep your signal-to-noise ratio under control.
- Continuous Asset Monitoring: Randori’s global network of dynamic cloud infrastructure continuously monitors and tracks asset changes and quickly alerts users when a critical issue is found.
- Shadow IT Discovery: Rich integrations and policy-driven rules engine make it easy to automate the discovery of Shadow IT.
- Risk-Based Vulnerability Prioritisation: Randori’s prioritisation engine combines the attacker’s perspective with business value, business impact, existing security controls, and remediation status to build a stack-ranked list of your most risky targets.
- Enterprise Integrations and Reporting: SIEM, SOAR, VM, asset management, and ticketing systems are critically important to effectively operationalising ASM. Randori’s out of the box integrations enable fast time to value
Using IBM Guardium and IBM Randori Together
7 in 10 organisations have been compromised by an unknown asset in the past year (2023). Having tools that can identify these assets provides organisations with the power to shut down access and fortify their weaknesses.
Having looked at the features and benefits of IBM Guardium and IBM Randori, we can see how using them together can be advantageous.
With focuses on different aspect of your IT and data infrastructures, utilising them in conjunction improves your oversight of attack surfaces and user access. Your IT estate is monitored for external threats and vulnerabilities, whilst your data is monitored and controlled against internal and external threats and anomalies.
Conclusion
There is no single silver bullet that will automatically lock down your IT landscape and attack surfaces, but knowing effort needs to be applied is a great place to start. Being aware of vulnerabilities means you can be prepared in the case of attack.
The focus on cybersecurity is on the rise, but this does not take away from the focus on cost and business efficiency or regulatory compliance. Having tools that can address all these business priorities at once is valuable.
Cyber Security
IBM Guardium and IBM Randori are two products that can largely increase your cyber awareness so you can apply effort and resources to the appropriate vector. When a breach does occur, your teams are efficiently alerted to the issue so they can focus on remediation.
No longer spend 277 days at the mercy of a data breach; see exactly where the breach is likely to or has occurred.
Save cost and effort, protect your brand reputation, and ensure regulatory compliance.
Compliance
Not only will your organisation be aware of attack vulnerabilities, but they can reduce the time taken to respond to audit requests with all the necessary data available through automated workflows.
Don’t just be compliant; prove it, efficiently.
Responsiv x Cybersecurity
Responsiv has a wealth of skills utilising IBM Guardium and IBM Randori. Responsiv Consulting partner with your teams to configure your solution in line with specific policies and regulations to ensure the software is running as expected.
With keen understanding of industry specific and industry agnostic regulations, we can help ensure your data, data storage and environments are compliant.
Check out our presentation on securing critical data for regulatory compliance, including SOX, GDPR, PCI DSS, HIPAA, and CCPA.
Responsiv take cyber security seriously and understand the business imperative. This is why we built the Responsiv Cloud Security Service; allowing organisations to set up their cloud security and user access the way they desire, knowing it is still secure.
We can work together to apply these products into your IT landscape to reduce your cybersecurity vulnerabilities across your organisation; on-prem or in the cloud.
Get in touch today to find out how Responsiv can help secure your IT landscape!